The Security Layer Between Your AI Agents and the Internet
Pipelock gives security teams an enforcement and inspection boundary for AI agent traffic across HTTP, WebSocket, and MCP.
Why teams are evaluating agent egress controls now
- Agents now have credentials, tool access, and outbound network reach.
- Prompt injection and poisoned tools can turn normal workflows into exfiltration paths.
- Most teams still lack a dedicated boundary that inspects and controls what agents send out.
What Pipelock Is
Pipelock sits between the agent and external systems. It combines traffic inspection with built-in process containment (Linux and macOS) in a single binary. It does not replace model guardrails. It adds a separate runtime security layer covering both the network boundary and OS-level containment.
Agent (secrets, no network) → Pipelock (inspection + policy) → Internet / MCP / APIsThe agent process keeps the credentials but cannot reach the internet directly. Pipelock has full network access but holds no agent secrets. This separation is enforced at the deployment layer: Docker networking, Kubernetes NetworkPolicy, iptables, or macOS PF.
What Pipelock is designed to reduce
Credential exfiltration. 46 DLP patterns across URLs, headers, and request bodies. Decodes base64, hex, URL-encoding, and Unicode evasion before matching. Catches environment variable leaks and secrets split across multiple requests.
Prompt injection in fetched content and tool responses. 6-pass normalization pipeline handles zero-width characters, homoglyphs, leetspeak, and encoded payloads. Scans HTTP responses, MCP tool results, and WebSocket frames.
SSRF and metadata endpoint access. Blocks private IPs, link-local addresses, and cloud metadata endpoints. DNS rebinding protection with post-resolution IP validation.
MCP tool poisoning and rug-pulls. Scans tool descriptions for hidden instructions. Detects mid-session description changes. 17 pre-execution policy rules block dangerous tool calls including reverse shells, credential file access, and persistence mechanisms.
Agent-driven crypto abuse patterns. Address poisoning detection for ETH, BTC, SOL, and BNB with allowlist and similarity scoring. BIP-39 seed phrase detection with dictionary lookup and checksum validation.
Fits into existing agent workflows
| Mode | What It Does |
|---|---|
| Proxy | Outbound HTTP/HTTPS scanning via HTTPS_PROXY. Optional TLS interception for full body inspection in CONNECT tunnels. |
| MCP proxy | Wraps stdio, Streamable HTTP, or WebSocket MCP servers with bidirectional scanning. Tool arguments, responses, and descriptions all inspected. |
| IDE integrations | One command for Claude Code, Cursor, or VS Code. Hooks or config wrapping, depending on IDE capabilities. |
| Scan API | POST /api/v1/scan evaluates URLs, text, or tool calls out-of-band. For orchestrators, CI/CD, SIEM, and approval workflows. |
| Process sandbox | pipelock sandbox -- COMMAND wraps any process with Landlock, seccomp, and network namespace isolation (Linux) or sandbox-exec profiles (macOS, alpha). Per-agent profiles with named filesystem grants. |
| Reverse proxy | pipelock run --reverse-proxy scans request and response bodies for any upstream HTTP service. |
| Config scoring | pipelock audit score evaluates security posture across 12 categories (0-100 letter grade). |
| Attack simulation | pipelock simulate runs 31 built-in attack scenarios against your running config (expands with canary tokens). |
Use proxy mode in the data plane. Use Scan API when you need a verdict service in the control plane. Use sandbox mode when the agent process needs OS-level containment.
Built for evaluation, control, and auditability
- Fail-closed behavior on parse errors, context cancellation, timeouts, and ambiguous state. Pipelock never returns “allow” on uncertainty.
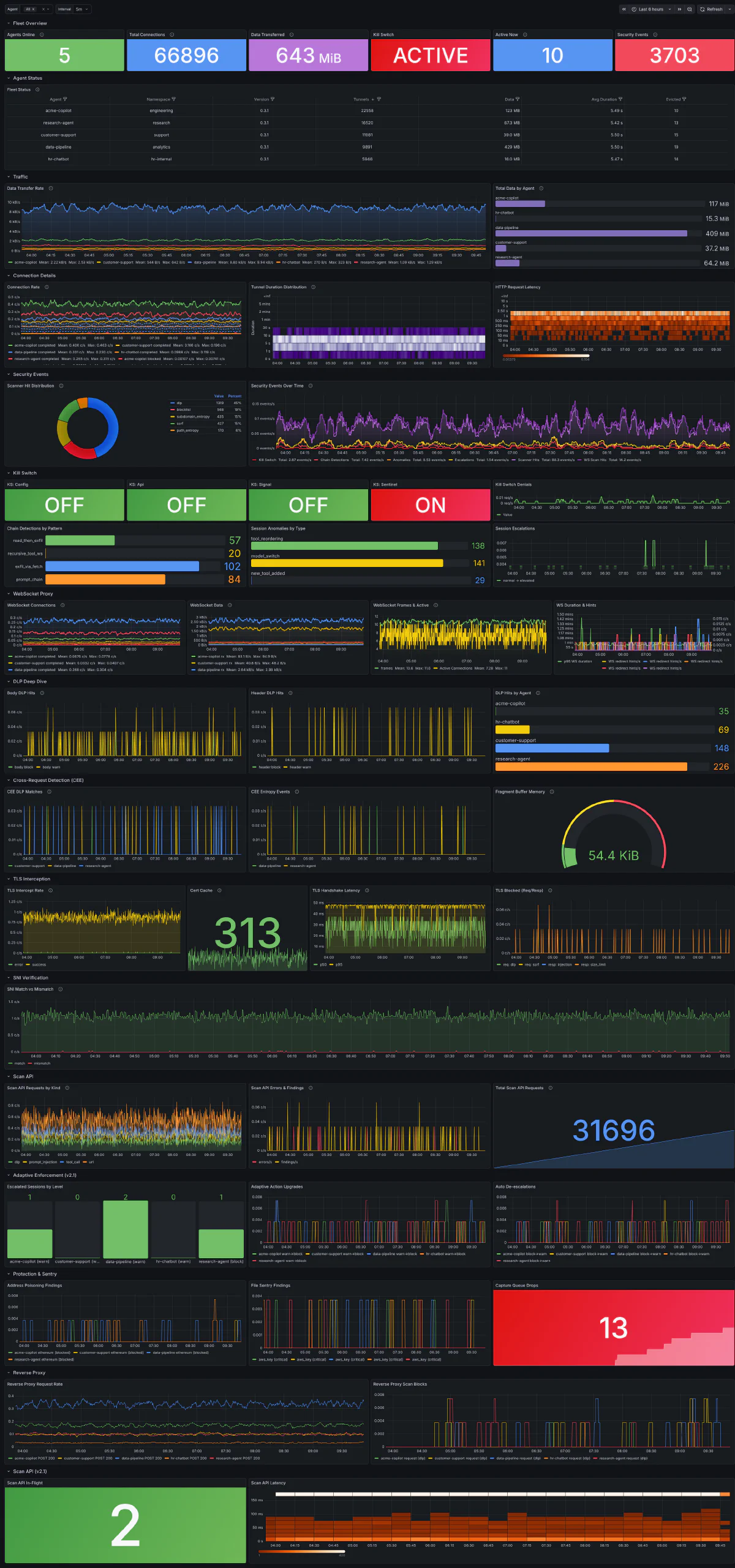
- Structured audit logs with MITRE ATT&CK technique IDs on blocked and anomaly findings. Webhook, syslog, and OTLP emission. 40 Prometheus metric families.
- Policy enforcement at runtime, not just prompt-time guidance. Domain allowlists, DLP scanning, tool policy rules, and rate limiting enforced at the network boundary.
- Signed artifacts with cosign signatures, CycloneDX SBOM, and SLSA v1.0 provenance attestation on every release.
- Flight recorder with hash-chained, tamper-evident audit log. SHA-256 chain links make any tampering detectable. Optional Ed25519 checkpoint signatures.
- Signed security assessments via
pipelock assess. HTML and JSON reports with Ed25519 signatures, compliance evidence mapped to OWASP MCP Top 10, Agentic Top 10, MITRE ATLAS, EU AI Act, and SOC 2. - Session manifests and signed decision records capture policy state, tool inventory, and verdict summaries with cryptographic proof of each enforcement action.
- Agent Bill of Materials (CycloneDX 1.6) with declared vs observed views and confidence scoring for runtime inventory.
- Documented limitations and honest gap analysis. Published OWASP coverage mappings with per-threat assessments.
Serious engineering, not a demo
- 8,800+ tests with race detection across all proxy, scanner, MCP, and policy paths
- Private adversarial testing (1,000+ private security tests) against the production binary before every release
- Cross-platform release validation (Linux, macOS, Windows on amd64 + arm64)
- Open source core with public docs, threat model, and evasion resistance test matrix
- Single static binary, ~18MB, 17 direct Go dependencies
Where Pipelock fits in a defense-in-depth stack
| Layer | What It Does | Example |
|---|---|---|
| Container / VM isolation | Isolates the agent from the host OS | Docker, gVisor, Firecracker |
| Process containment | Restricts filesystem, syscalls, and network at the OS level | Pipelock sandbox (Linux + macOS alpha), NemoClaw/OpenShell |
| Guardrails | Influences model behavior inside the inference pipeline | NeMo Guardrails, LlamaFirewall |
| Traffic boundary | Inspects and controls what the agent sends over the network | Pipelock proxy |
Pipelock combines both the process containment layer and the traffic boundary in a single binary. Container isolation and guardrails remain complementary. A container restricts host access. Guardrails shape model outputs. Pipelock handles what the process can touch and what goes out over the wire.
Mapped to how enterprise evaluators think
Pipelock publishes detailed mappings against the OWASP Agentic AI Top 10, OWASP LLM Top 10, OWASP MCP Top 10, NIST 800-53 security controls, and EU AI Act compliance requirements. These are available in the public repo documentation.
For analyst-friendly evaluation frameworks, Pipelock addresses:
- Runtime guardrails: scanning and policy enforcement on live agent traffic
- Data protection: DLP, entropy analysis, environment variable leak detection, cross-request fragment tracking
- Tool/plugin security: MCP tool poisoning detection, rug-pull detection, session binding, tool policy rules
- Audit and compliance: structured logging, MITRE ATT&CK mapping, signed reports, Prometheus metrics
Typical evaluation scenarios
- Teams deploying AI coding agents internally (Claude Code, Cursor, VS Code)
- Enterprises adopting MCP-based tooling across multiple teams
- Security teams reviewing agent egress risk as part of a broader AI governance initiative
- Control-plane builders who need a verdict service via API for pre-execution policy decisions
Evaluating Pipelock for your team?
We can help scope deployment mode, logging, and policy fit for your environment.