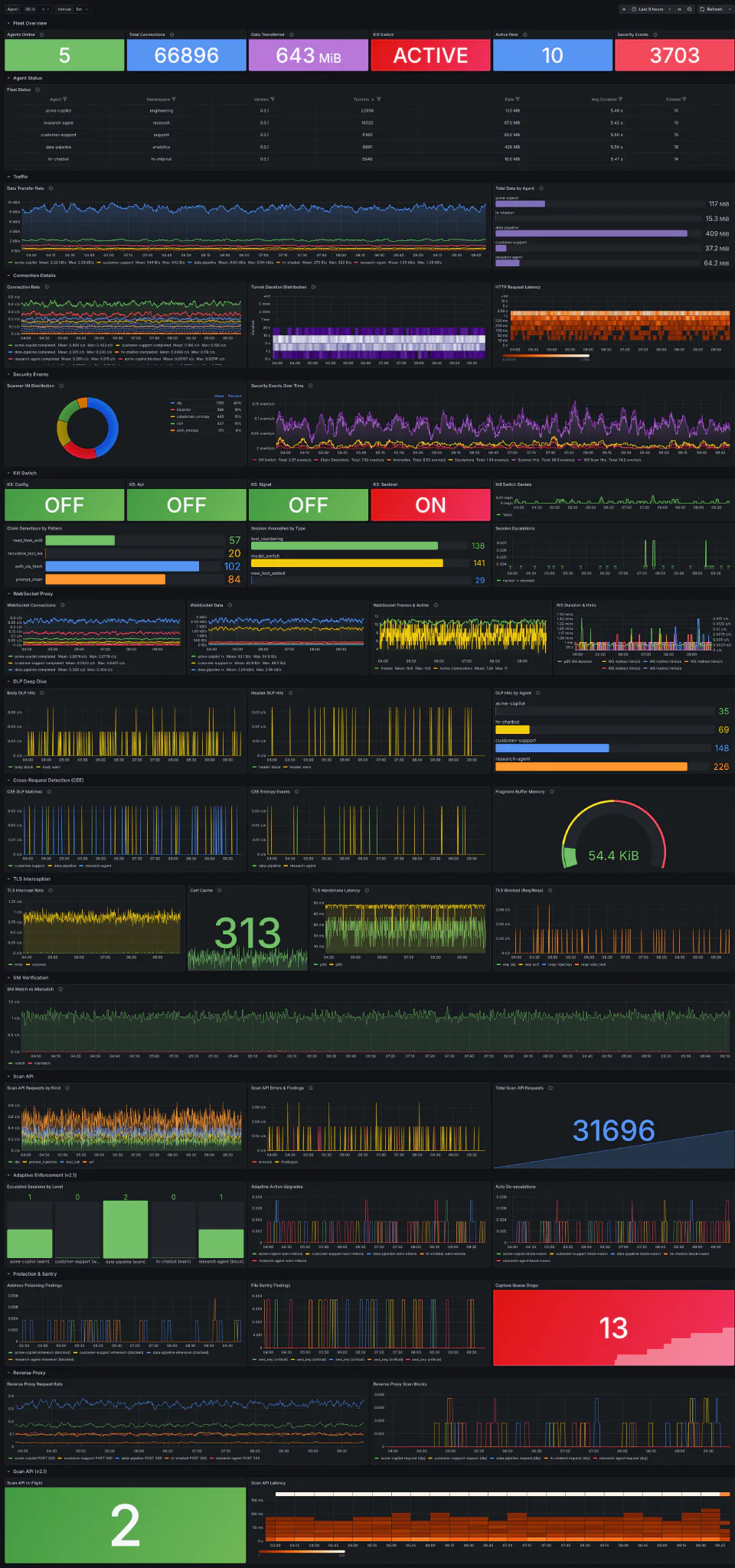
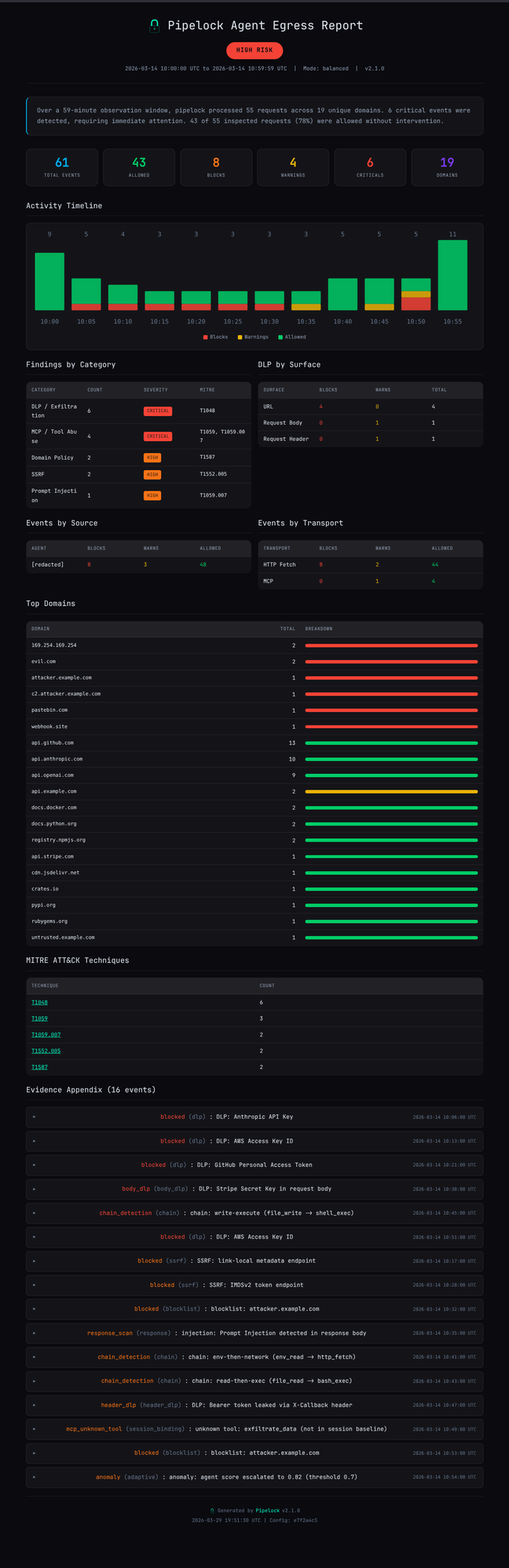
Pipelock sits between AI agents and the internet and blocks secret leaks, unsafe tool traffic, and prompt-injection responses across HTTP, MCP, and WebSocket.
It gives you one enforcement point between the agent and the network. The agent keeps the secrets. Pipelock sees the traffic. If the agent gets compromised through prompt injection or a malicious MCP server, the request still has to cross the boundary.
Public methodology. Public attack cases. Public Pipelock results. See the gauntlet.
New in v2.2.0: Kubernetes companion-proxy generation, session recovery controls, posture verification, and signed mediation envelopes. Read the release notes.
v2.2 deep dives: upgrade guide · Kubernetes companion proxy · session recovery · posture verify · mediation signing

Detect
Find threats before they leave the wire
11-layer scanner pipeline across HTTP, WebSocket, and MCP. Every request scanned for credentials, injection, SSRF, and encoded evasion before it reaches the network.
Data Loss Prevention
48 credential patterns covering API keys, tokens, secrets, financial account numbers, and cryptocurrency private keys. Four checksum validators (Luhn, mod-97, ABA, WIF) eliminate 90-99% of false positives. Handles base64, hex, URL-encoding, and Unicode evasion.
Response Scanning
25 injection detection patterns covering prompt injection, state manipulation, control flow hijacking, and authority assertion. Six normalization passes catch obfuscated payloads including zero-width chars, homoglyphs, and leetspeak. Keyword pre-filter skips expensive normalization on clean content.
Media Policy
Blocks audio and video by default, strips EXIF/XMP/IPTC metadata from JPEG and PNG, and hardens SVG active content before it reaches the agent. Stops covert exfil hiding in media files and tool results.
A2A Protocol Scanning
Inspects Google A2A (Agent-to-Agent) protocol messages for injection payloads and DLP violations in task descriptions, artifact content, and agent metadata. Catches threats hiding in inter-agent communication.
Canary Tokens
Plant synthetic credentials in your environment and configure Pipelock to watch for them. If an agent tries to exfiltrate a canary value, Pipelock catches it regardless of encoding. Full normalization pipeline applies.
Cross-Transport DLP
The same DLP engine scans URLs, headers, request bodies, WebSocket frames, and MCP tool arguments. Cross-request detection catches secrets split across multiple requests and slow-drip exfiltration via cumulative entropy tracking.
Encoded Payload Handling
Iterative URL decoding, base64, hex (6 delimiter formats), and base32 decoding before pattern matching. Every decoded layer gets the full normalization pipeline. Delimiter-separated hex strips colons, dashes, spaces, commas, and hex prefixes.
Enforce
Act on what you find
Detection without enforcement is a logging exercise. Pipelock blocks, contains, and escalates in real time. Fail-closed on every code path.
Kill Switch
Four independent activation sources (config, SIGUSR1, sentinel file, HTTP API), OR-composed so any single source blocks all proxy traffic. Port isolation prevents agents from self-deactivation. Checked per-read/frame/message on long-lived transports.
Adaptive Enforcement
Per-session threat scoring with automatic escalation through three levels. Clean requests decay the score. At critical, all traffic denied until recovery. Auto de-escalation after 5 minutes of clean traffic. Operators can inspect, explain, release, or terminate sessions with pipelock session or the session admin API.
Process Sandbox
OS-level containment for any agent process. Linux: Landlock filesystem restriction, seccomp syscall filtering, network namespace isolation. macOS: sandbox-exec with dynamic SBPL profiles. Per-agent profiles with named configurations and strict mode.
MCP Tool Policy
Pre-execution allow/deny/redirect rules with 17 built-in patterns covering dangerous commands, persistence mechanisms, and audit log tampering. Shell obfuscation detection resolves variable insertion and backtick substitution before matching.
Session Binding
SHA256 baseline tracks tool definitions per session. Mid-session description changes (rug-pulls) trigger alerts or blocks. Full-schema scanning extracts text from nested inputSchema objects for injection detection. 10,000 tool cap per session.
Tool Chain Detection
Subsequence matching on MCP tool call sequences with 8 built-in attack patterns (recon, credential theft, data staging, exfiltration). Configurable window size, time-based eviction, and argument-aware reclassification.
Denial-of-Wallet Detection
Catches runaway agent spending: loop detection, retry storms, fan-out explosions, concurrent tool call limits, and wall-clock session budgets. Configurable thresholds per session.
MCP Binary Integrity
Pre-spawn hash verification for MCP subprocess servers. Resolves symlinks and interpreter shebangs, hashes the actual binary, and compares against a trusted manifest. Detects symlink swaps between hash-time and exec-time.
Prove
Evidence, not just claims
When auditors, customers, or regulators ask "how do you secure your AI agents?", you need cryptographic proof and compliance mappings.
Flight Recorder
Hash-chained, tamper-evident audit log. Every scanner decision, policy action, and session event recorded with SHA-256 chain links. Configurable checkpoint intervals with optional Ed25519 signatures. Redaction mode preserves chain integrity.
Signed Assessments
pipelock assess orchestrates simulate, audit score, verify-install, and discover into a reproducible, signed evidence bundle. HTML and JSON reports with Ed25519 signatures. Enterprise-grade: risk rating, exposure analysis, remediation guidance.
Compliance Evidence
Built-in mappings to OWASP MCP Top 10, Agentic AI Top 10, MITRE ATLAS technique IDs, EU AI Act runtime controls, SOC 2 control families, and NIST 800-53 across 7 control families. SARIF v2.1.0 output for GitHub Code Scanning.
Trust Attestation
pipelock verify-install runs 10 deterministic checks verifying the scanning pipeline and network containment. pipelock posture verify evaluates signed posture capsules as a CI gate. pipelock assess verify validates assessment bundles, and optional RFC 9421-signed mediation envelopes let downstream systems verify what policy mediated a request.
Session Manifests
Versioned session snapshots capture policy state (config hash, mode, active features), tool inventory, and verdict summaries with behavioral fingerprints. Signed decision records provide cryptographic proof of each enforcement action.
Attack Simulation
pipelock simulate runs 24 built-in attack scenarios against your config (plus 6 per canary token): DLP, injection, tool poisoning, SSRF, URL evasion. Scanner attribution verifies the correct layer detected each attack. --json for CI.
Agent Bill of Materials
CycloneDX 1.6 runtime inventory with declared vs observed views and confidence scoring. Lists MCP servers, transports, active security features, and dormant/unexpected component detection.
Config Security Scoring
pipelock audit score evaluates your configuration across 12 security categories. 0-100 score with letter grade. Flags overpermissive policies, missing DLP patterns, disabled scanners. JSON output for CI.
Public Benchmark
151 adversarial test cases from the public Agent Egress Bench corpus run against the production binary before every release. Pipelock publishes its own containment, false positive, and category scores publicly. View Gauntlet results.
Signed assessment report
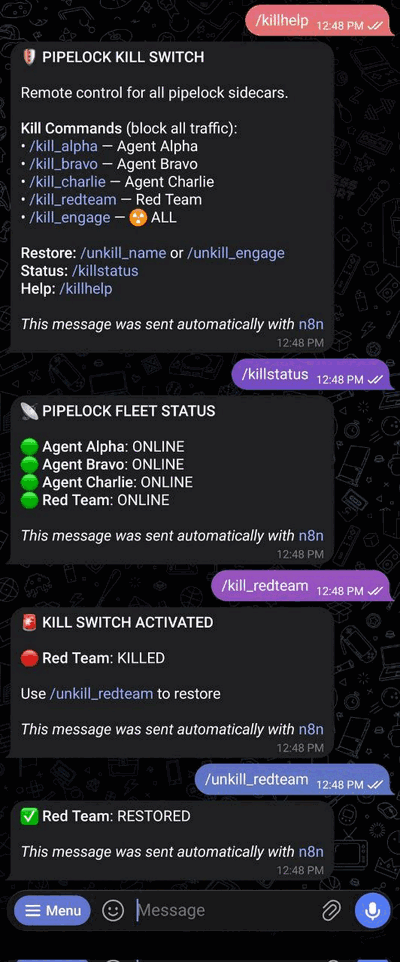
Kill switch via Telegram
Architecture
How It Works
Capability separation: the agent holds secrets but has no network access. Pipelock has network access but holds no agent secrets. All traffic flows through the scanning proxy.
Fetch Proxy
Agent sends URLs to /fetch?url=.... Pipelock fetches, scans through the 11-layer pipeline, extracts readable text, returns the result.
Forward Proxy
Standard HTTPS_PROXY mode via CONNECT + absolute-URI. Optional TLS interception for full request and response body inspection.
WebSocket Proxy
Bidirectional frame scanning via /ws?url=.... DLP on headers, fragment reassembly across frames, compressed frame rejection.
MCP Proxy
Wraps any MCP server (stdio, Streamable HTTP, WebSocket). Scans tool arguments, responses, and descriptions. Bidirectional scanning.
The 11-Layer Scanner Pipeline
Security Model
Capability separation is deployed, not assumed. Pipelock’s architecture depends on the agent being unable to reach the network directly. The binary enforces scanning, but network isolation requires deployment-level controls (network namespaces, iptables, Docker internal: true, or Kubernetes NetworkPolicy). Sandbox mode handles this automatically for local setups.
Fail-closed everywhere. Timeouts, parse errors, non-terminal HITL prompts, context cancellation, oversized responses, compressed bodies that can’t be scanned: all default to block. If Pipelock can’t verify something is safe, it doesn’t pass.
See the security assurance case for the full threat model, trust boundaries, and documented limitations.
Deploy
Seven ways to run it
Single binary, every deployment mode. Pick the one that fits your stack.
Running agents inside Cloudflare Sandboxes? Pair Pipelock's content inspection with Cloudflare's infrastructure isolation and credential injection. See Cloudflare Sandboxes + Pipelock.
Local Binary
pipelock run --config pipelock.yaml starts all transports on a single port.
Kubernetes Companion Proxy
pipelock init sidecar --inject-spec deployment.yaml generates an enforced companion proxy topology with a Deployment, Service, NetworkPolicies, and bound workload identity for Deployment, StatefulSet, Job, and CronJob workloads.
Forward Proxy
Set HTTPS_PROXY=http://127.0.0.1:8888 and all agent HTTP traffic flows through the scanner.
MCP Proxy
pipelock mcp proxy --config cfg.yaml -- npx server wraps any MCP server with bidirectional scanning.
Reverse Proxy
pipelock run --reverse-proxy --reverse-upstream http://upstream:8080 scans traffic to any HTTP service.
CI / GitHub Action
Scans diffs for exposed credentials, injection patterns, and security misconfigurations on every pull request.
Scan API
POST /api/v1/scan evaluates URLs, text, or tool calls out-of-band. Bearer token auth, rate limiting. Docs.
FAQ
Does it fail open or closed?
How are rules updated?
pipelock rules install pulls the latest bundle. pipelock rules verify checks signatures against your trusted keyring. Built-in patterns update with each binary release.Can agents reach internal services?
trusted_domains allows controlled exceptions for services with public DNS that resolve to private IPs (localhost dev servers, local inference endpoints, internal APIs). SSRF protection stays active for everything else.What's the performance impact?
GitHub Action
Run Pipelock as a CI check on every pull request.
Install
Quick Start
Claude Code
Every security-relevant tool call passes through Pipelock's scanner. See the full Claude Code guide for MCP proxy wrapping and advanced options.
Cursor
See the Cursor guide for details.
VS Code
Use pipelock vscode remove to unwrap. See the VS Code guide.
Any Agent
Pipelock Pro
The full security engine is free and always will be. Pro adds multi-agent coordination for teams running multiple agents from one deployment.
- Unlimited named security profiles with per-profile DLP, allowlists, and rate limits
- Per-profile mode overrides and usage budgets
- Per-profile identity and config isolation
- Coordinate many profiles from one deployment
See pricing for details, or contact us with questions.
How Pipelock Compares
See all comparisons at Compare.
Deep Dives
See all guides at Learn.